Order Now. Use Coupon 1346 to get the softcover for $99. (Regular price $179.)
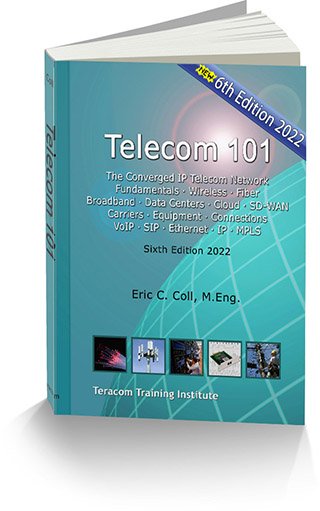
Packed with information, authoritative, up to date, covering all major topics – and written in plain English – Telecom 101 is an invaluable textbook and day-to-day reference on telecommunications for non-engineers.
This is the best comprehensive book on telecommunications available anywhere: based on the course materials for Teracom’s famous instructor-led Course 101 Broadband, Telecom, Datacom and Networking for Non-Engineers, the selection of content, its order, timing and pacing have been tuned, refined and constantly updated over years to effectively define and deliver the core set of technical knowledge needed by anyone serious in the telecom business today.
Telecom 101 Sixth Edition is right up to date with discussion of aircraft interfering with 5G in the C-band.
Telecom 101 covers the technologies, the players, the products and services, jargon and buzzwords, and most importantly, the underlying ideas… and how it all fits together.
In one book, you get consistency, completeness and unbeatable value: a wealth of clear, concise, organized knowledge, impossible to find in one place anywhere else!
Reviewing the Telecom 101 Table of Contents, you’ll find that many chapters are like self-contained reference books on specific topics; get all of these topics bound in one volume for one low price.
Compare this to hunting down and paying for multiple books by different authors that may or may not cover what you need to know- and you’ll agree this is a very attractive deal.
Telecom 101 is an economical and convenient way to self-study… these are the materials to an instructor-led course that costs $1895 to attend.
Written by our top instructor, Eric Coll, M.Eng., Telecom 101 contains decades of knowledge and learning distilled and organized into an invaluable study guide and practical day-to-day reference for non-engineers: career- and productivity-enhancing training… an investment in life-long knowledge that will be repaid many times over.
Order softcover now
Use coupon 1346 for the Solstice Sale price of $99
Plus 7.95 shipping to US lower 48 States and Canadian provinces
Sale ends after the big party that caps off the week of solstice feasting (Jan 2)
Hardcover Telecom 101 is also on sale
eBook: available on Amazon, Google and Apple
Join thousands of satisfied customers. Get your copy today!