Next Boot Camp Live Online Mar 15-19, 2021 9am-5pm ET (GMT-5)
Reserve your spot now before the class fills up.

Telecommunications Training Blog
Tutorials and articles from Teracom Training Institute. Bringing you the best in telecom training and certification since 1992.
Enjoy this free sample from CNTS – Certified Network Telecommunications Specialist
Course 2213 IP Addresses, Packets and Routers
Lesson 1 – Introduction to IP Addresses, Packets and Routers
Course 2213 IP Addresses, Packets and Routers
IP Addresses • Packets • Networks • Routers • Static and Dynamic Addresses • DHCP • Public and Private Addresses • NAT • IPv6
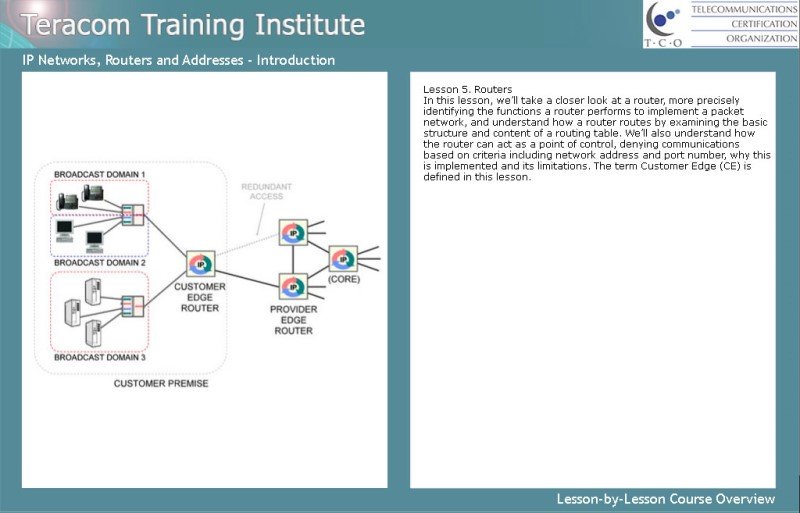
IP Networks, Routers and Addresses is a comprehensive course on IP networking fundamentals: IP packets, IP addressing and IP routers.
We’ll see how routers implement the network with packet-switching, that is, relaying packets from one circuit to another, and how routers are a point of control for network security. We’ll introduce the term Customer Edge (CE), and understand the basic structure and content of a routing table.
Then we’ll cover the many aspects of IP addressing: IPv4 address classes, dotted decimal, static vs. dynamic addresses, DHCP, public vs. private addresses, Network Address Translation, and finish with an overview of IPv6.
Course Lessons
Based on Teracom’s famous Course 101, tuned and refined over the course of 20 years of instructor-led training, we’ll cut through the jargon to clearly explain IP and routers, packets and addresses, the underlying ideas, and how it all works together… in plain English.
Register a group of 2 or more for one of these courses at the same time and receive a discount.
Applies to Bootcamp, Course 101 or Course 130
Discounts
2-3 persons: 10% discount each.
4 persons: 20% discount each.
5 or more persons: 25% discount each.

The TCO Certified Telecommunications Subject Matter Expert (CTSME) is the most comprehensive telecom, datacom, networking, wireless, VoIP and SIP training and certification available anywhere.
Teracom Training continues to update the training material for the 2020s.
The CTSME Certification Package includes four TCO Certification Packages: CTNS, CVA, CWA and CTA, with unlimited repeats and no time limits, the distinctive Certified Telecommunications Subject Matter Expert CTSME Certification and a signed, sealed and framed certificate for $1495.
Here’s what you get:
CTA Certification Package Unlimited Plan. 16 courses covering all major topics in telecom, datacom and networking from POTS to MPLS plus the Security module.
CVA Certification Package Unlimited Plan. Six courses providing depth on Voice over IP from packetization to SIP trunking.
CWA Certification Package Unlimited Plan. Three in-depth courses on wireless including spectrum, propagation, cellular and mobility, Bluetooth, Wi-Fi and more.
CTNS Certification Package Unlimited Plan. CTNS is a subset of CTA, six of the sixteen CTA courses and exams – yet recognized as the #1 telecommunications certification worldwide and a valuable credential to add to your résumé.
We are so confident of the quality of the training, it comes with a 30‑day no questions asked 100% money‑back guarantee.
Terms and Conditions:
Buy CTNS, CTA, CVA and CWA at the same time and receive the special bundle price OR buy the certifications one by one and the upgrade to the CTSME certification at the special bundled price when you are ready.


New Course 2241 Introduction to Broadband Telecommunications along with existing Course 2221 Fundamentals of Voice over IP will be added to the CTNS Certification Package before year-end.
The price of the CTNS package will increase when the number of courses increases from six to eight. Since all existing customers will automatically get the two new courses at no additional charge, you can beat the price increase by purchasing CTNS before the upgrade and get the two new courses, when they are released, for free!
Course 2206 Wireless Telecommunications has received a major update including 5G, Wi-Fi 6 (802.11ax) and more. Free access for current customers.
Updates of TCO Certification courses continue to roll out with a major new release of Course 2206 Wireless Telecommunications, a comprehensive course on wireless, including radio fundamentals, cellular and mobile telecommunications, LTE, 5G, Wi-Fi 6 (802.11ax) and more.

All current customers will automatically see the updated version in their dashboard.
If you’re not already registered for this course, we invite you to join the many people who have benefited from gaining these knowledge skills… and TCO Certification to prove it!
Taking this course, you will develop a solid understanding of the fundamental principles of radio, mobility and cellular, network components and operation, digital radio, mobile phone calls and mobile Internet access, spectrum-sharing technologies like OFDM, and LTE and 5G. In addition, you will get up to speed on the components, operation and latest standards for Wi-Fi, and the essentials of satellite communications.
We’ll cut through the jargon to demystify wireless, explaining the fundamentals of cellular and mobility, the buzzwords, the network, technologies and generations, the underlying ideas, and how it all works together… in plain English.
Course
Lessons
1. Introduction (free sample lesson)
2. Mobile Network Components, Jargon and Operation
3. Cellular Principles
4. PSTN Phone Calls using the Phone App: Voice Minutes
5. Mobile Internet: Data Plan
6. Spectrum-Sharing: FDMA, TDMA, CDMA, OFDM
7. 4G LTE: Mobile Broadband
8. 5G New Radio: Enhanced Mobile Broadband, IoT Communications
9. Wi-Fi: 802.11 Wireless LANs (free sample lesson)
10. Communication Satellites
detailed course description • very detailed PDF brochure • register
Course 2206 Wireless Telecommunications is available on its own, or included in CTNS, CTA and CTSME Certification Packages.
The full lesson free, in full quality, with our compliments.
Lesson 9 from the new release of Course 2206 Wireless Telecommunications